Code Obfuscation

Quick Navigation:
- Code Obfuscation Definition
- Code Obfuscation Explained Easy
- Code Obfuscation Origin
- Code Obfuscation Etymology
- Code Obfuscation Usage Trends
- Code Obfuscation Usage
- Code Obfuscation Examples in Context
- Code Obfuscation FAQ
- Code Obfuscation Related Words
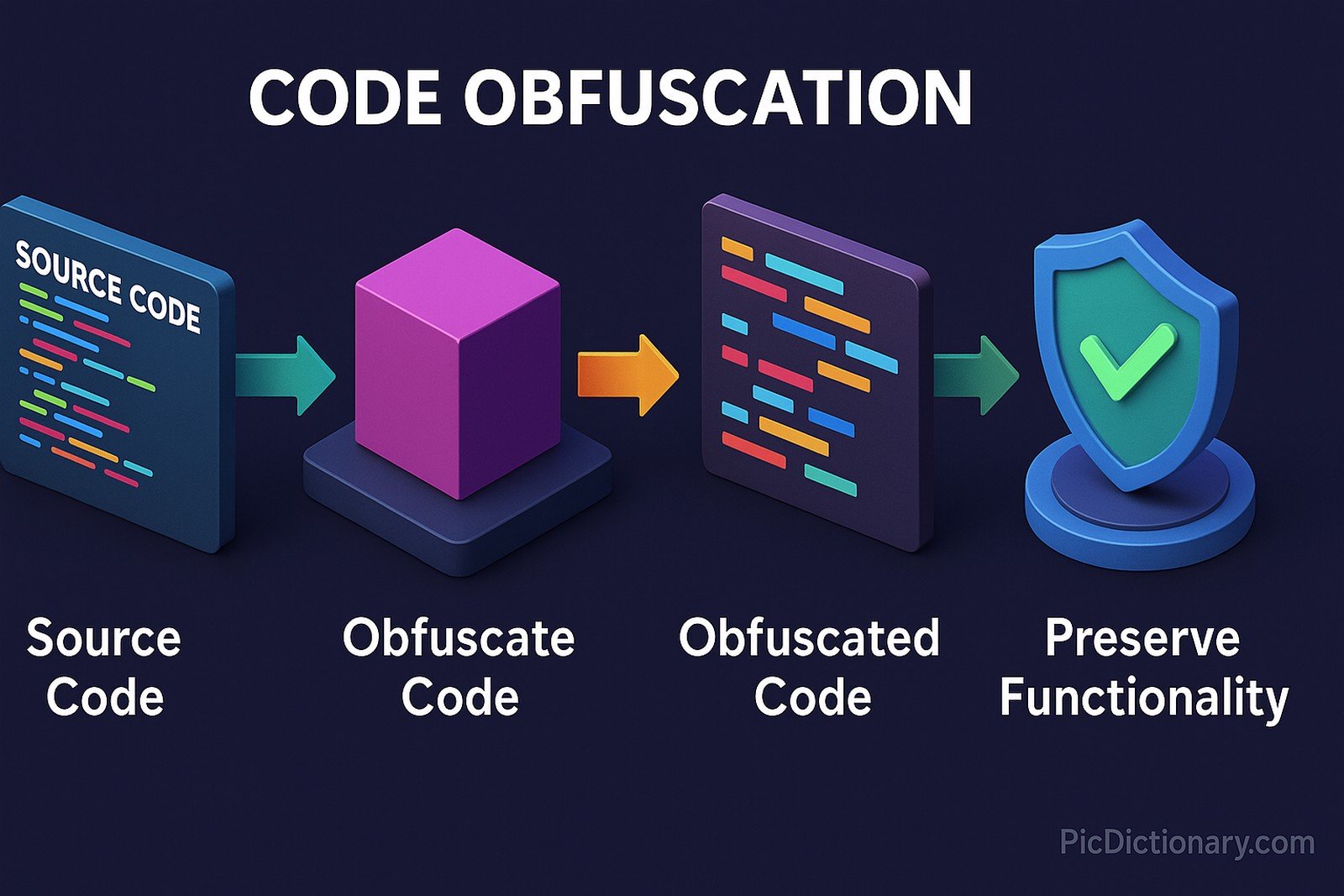
Code Obfuscation Definition
Code obfuscation is the process of transforming software code into a more complex and unintelligible format while preserving its original functionality. This technique is primarily used to protect intellectual property, prevent reverse engineering, and enhance software security. Obfuscation methods include renaming variables and functions, inserting dummy code, and altering control flow structures. Many programming languages support code obfuscation tools, which make it difficult for attackers to analyze or tamper with the software.
Code Obfuscation Explained Easy
Think of code obfuscation like a secret message written in a scrambled way—only the person with the key knows how to read it. Just like you might use a secret code with your friends to hide your notes, programmers scramble their software to stop bad guys from understanding it. Even though the code looks messy and confusing, it still works the same way when the computer runs it!
Code Obfuscation Origin
The concept of code obfuscation dates back to the early days of computing when developers sought ways to protect proprietary software from unauthorized modifications and piracy. With the rise of software reverse engineering techniques, obfuscation became an essential tool for securing applications, especially in commercial and enterprise environments.
Code Obfuscation Etymology
The term "obfuscation" comes from the Latin word obfuscare, meaning "to darken" or "to make unclear." It refers to the practice of making software code difficult to understand by modifying its structure while keeping its intended functionality intact.
Code Obfuscation Usage Trends
With the increasing threat of software piracy, malware analysis, and cyberattacks, code obfuscation has gained prominence in software security. It is widely used in mobile applications, cloud-based services, and digital rights management (DRM) solutions. Many companies integrate obfuscation techniques into their software development pipelines to safeguard proprietary algorithms and prevent unauthorized access.
Code Obfuscation Usage
- Formal/Technical Tagging:
- Software Security
- Reverse Engineering Prevention
- Intellectual Property Protection - Typical Collocations:
- "obfuscated code"
- "code obfuscation techniques"
- "reverse engineering protection"
- "secure software development"
Code Obfuscation Examples in Context
- A game development company applies code obfuscation to protect its game logic from hackers trying to cheat.
- Banking applications use obfuscation to prevent cybercriminals from analyzing and exploiting security vulnerabilities.
- Mobile app developers obfuscate their Android applications to reduce the risk of unauthorized modifications and data theft.
Code Obfuscation FAQ
- What is code obfuscation?
Code obfuscation is a technique that modifies software code to make it difficult to understand while maintaining its functionality. - Why is code obfuscation used?
It is used to protect software from reverse engineering, intellectual property theft, and malicious tampering. - Does obfuscation affect software performance?
In some cases, heavy obfuscation can slightly impact performance, but optimized techniques ensure minimal overhead. - What are common code obfuscation techniques?
Techniques include variable renaming, control flow obfuscation, dummy code insertion, and string encryption. - Can obfuscated code be reversed?
While obfuscation makes code analysis harder, skilled attackers can sometimes de-obfuscate it using advanced tools. - Is obfuscation the same as encryption?
No, encryption secures data by making it unreadable without a decryption key, while obfuscation only makes code harder to understand. - Which programming languages support obfuscation?
Most modern languages, including Java, C++, Python, and JavaScript, have obfuscation tools. - Do companies use obfuscation for open-source projects?
Typically, no. Open-source projects rely on transparency, so obfuscation is mainly used in proprietary software. - Can obfuscation help prevent software piracy?
Yes, it makes it harder for unauthorized users to modify or crack software. - Is code obfuscation legal?
Yes, obfuscation is a common and legal security practice used by developers to protect their software.
Code Obfuscation Related Words
- Categories/Topics:
- Software Security
- Cybersecurity
- Software Development
Did you know?
One of the most famous examples of code obfuscation was in malware development. Some viruses and Trojans use extreme obfuscation techniques to avoid detection by antivirus programs, making cybersecurity researchers' jobs significantly more challenging.
PicDictionary.com is an online dictionary in pictures. If you have questions or suggestions, please reach out to us on WhatsApp or Twitter.Authors | Arjun Vishnu | @ArjunAndVishnu

I am Vishnu. I like AI, Linux, Single Board Computers, and Cloud Computing. I create the web & video content, and I also write for popular websites.
My younger brother, Arjun handles image & video editing. Together, we run a YouTube Channel that's focused on reviewing gadgets and explaining technology.



Comments powered by CComment