Rootkit Detection

(Representational Image | Source: Dall-E)
Quick Navigation:
- Rootkit Detection Definition
- Rootkit Detection Explained Easy
- Rootkit Detection Origin
- Rootkit Detection Etymology
- Rootkit Detection Usage Trends
- Rootkit Detection Usage
- Rootkit Detection Examples in Context
- Rootkit Detection FAQ
- Rootkit Detection Related Words
Rootkit Detection Definition
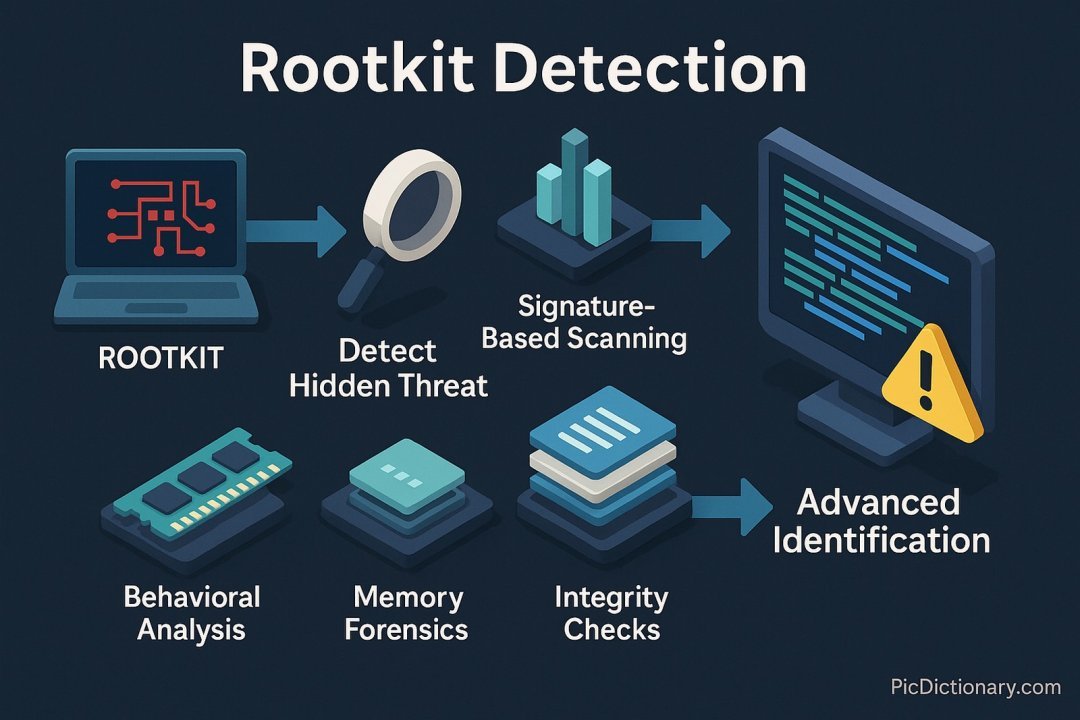
Rootkit detection refers to the methods and tools used to identify hidden, malicious software known as rootkits. Rootkits are designed to conceal their presence, making them difficult to detect using traditional antivirus solutions. Detection techniques include behavioral analysis, signature-based scanning, memory forensics, and integrity checks. Advanced rootkit detection tools scan system files, registry entries, and kernel memory to uncover hidden threats.
Rootkit Detection Explained Easy
Imagine a burglar sneaks into your house and hides under the floorboards, making sure you never notice them. Rootkits do the same thing but inside your computer, hiding from security programs. Rootkit detection works like a super flashlight that scans every hidden corner of your system to find and remove these digital intruders.
Rootkit Detection Origin
The concept of rootkit detection emerged as cyber threats became more sophisticated in the early 2000s. Initially, rootkits were used for legitimate purposes, such as remote administration, but cybercriminals repurposed them to hide malware. As a result, security researchers began developing advanced detection techniques to counter these stealthy threats.
Rootkit Detection Etymology
The term "rootkit detection" originates from "rootkit," a combination of "root" (referring to the highest user privilege in Unix-like systems) and "kit" (a set of tools). Detection methods aim to uncover and remove these hidden tools before they cause harm.
Rootkit Detection Usage Trends
Rootkit detection has become increasingly crucial due to the rise in stealth malware targeting operating systems and firmware. Security software vendors continuously develop new detection methods to counter evolving threats. Modern security solutions integrate artificial intelligence and machine learning to enhance rootkit identification.
Rootkit Detection Usage
- Formal/Technical Tagging:
- Cybersecurity
- Malware Analysis
- Digital Forensics
- Typical Collocations:
- "rootkit detection software"
- "kernel-level rootkit detection"
- "advanced malware detection techniques"
- "behavior-based rootkit detection"
Rootkit Detection Examples in Context
- A cybersecurity team uses memory forensics tools to perform rootkit detection on a compromised system.
- Modern antivirus programs integrate behavioral analysis for real-time rootkit detection.
- Digital forensic investigators rely on integrity checks to uncover hidden rootkits in system files.
Rootkit Detection FAQ
- What is rootkit detection?
Rootkit detection refers to the process of identifying and removing hidden malware designed to evade traditional security measures. - Why are rootkits difficult to detect?
Rootkits operate at a deep system level, often modifying core files and disguising themselves to avoid standard detection techniques. - What tools are used for rootkit detection?
Common tools include GMER, Rootkit Revealer, Malwarebytes Anti-Rootkit, and Microsoft's Windows Defender Offline. - Can rootkits be removed easily?
Some rootkits are deeply embedded, requiring specialized removal tools or even a complete system reinstallation. - What are common signs of a rootkit infection?
Symptoms include unusual system slowdowns, missing files, unexpected reboots, and antivirus software being disabled. - How does behavioral analysis help in rootkit detection?
Behavioral analysis identifies suspicious activity patterns instead of relying on known signatures, improving detection rates. - Are rootkits only found on Windows systems?
No, rootkits can also target Linux, macOS, and even firmware and hardware components. - What is kernel-level rootkit detection?
Kernel-level detection involves analyzing the core operating system functions to identify modifications caused by rootkits. - Can machine learning improve rootkit detection?
Yes, AI and machine learning can enhance rootkit detection by identifying new, unknown variants based on behavioral patterns. - Is rootkit detection included in standard antivirus software?
Many modern antivirus solutions include rootkit detection, but advanced tools may be required for deep scans.
Rootkit Detection Related Words
- Categories/Topics:
- Cybersecurity
- Malware Protection
- Digital Forensics
Did you know?
In 2005, Sony BMG faced backlash for secretly installing a rootkit on users' computers to enforce digital rights management (DRM). This unauthorized software left millions of systems vulnerable to security threats, highlighting the dangers of hidden rootkits and the need for advanced detection techniques.
PicDictionary.com is an online dictionary in pictures. If you have questions or suggestions, please reach out to us on WhatsApp or Twitter.Authors | Arjun Vishnu | @ArjunAndVishnu

I am Vishnu. I like AI, Linux, Single Board Computers, and Cloud Computing. I create the web & video content, and I also write for popular websites.
My younger brother, Arjun handles image & video editing. Together, we run a YouTube Channel that's focused on reviewing gadgets and explaining technology.



Comments powered by CComment